In security matters, the federal security clearance process will be overhauled this month. - The Office of Personnel Management (OPM) announced that it will establish the National Background Investigations Bureau (NBI). - The NBI will be a new federal office under the Department of Defense. - To discuss this further, Dan Verdun, executive editor at Mara talk, joins us. - Before moving forward, let's recap the reasons behind the creation of this new entity by OPM. - OPM had no choice but to create the NBI due to the compromise of over 21 million background investigations by Chinese hackers and potentially other foreign intelligence services. - OPM lacked the resources, technical expertise, and cybersecurity capabilities to protect this sensitive information. - Now, let's talk about how this new office will operate and who will be in charge. - The President will appoint the head of the NBI, who will report to the director of OPM. - The personnel responsible for conducting background investigations will likely transition from OPM to the new agency. - However, the major change is that the systems, databases, and protection of this information will be shifted from OPM to the Department of Defense. - The Department of Defense has cybersecurity expertise from agencies like the NSA to enhance the security measures. - Moving on, let's discuss the staffing and budgetary requirements for creating the NBI and whether the Obama administration will receive the necessary support from Congress. - It is estimated that they will request approximately $100 million to establish the NBI, and it is likely that they will receive the resources they need. - However, there is some resistance from Congress, questioning the need for creating a new bureaucracy. - Now, let's address the criticism from House Oversight and Government Reform Committee Chairman, Jason Chaffetz. - Chaffetz argues that simply creating a new government entity does not solve the problem. - He...
Award-winning PDF software





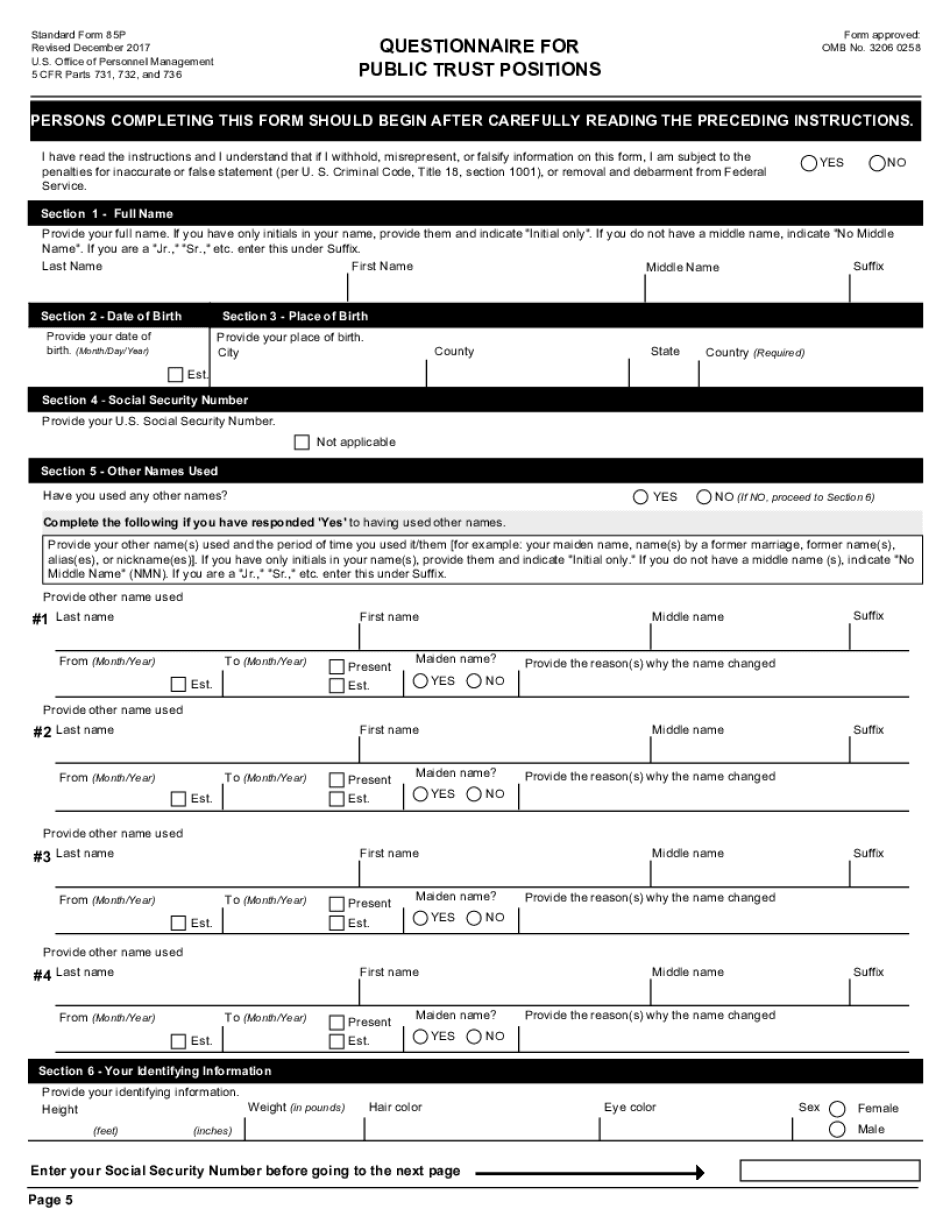
Sf 85p processing time 2017-2025 Form: What You Should Know
Sections 732, 731, and 736 apply only to positions for which a security clearance is required; for positions exempted from the clearance system by 5 CFR Parts 731 – 736, use the appropriate form. The authority for this form is 5 CFR Parts 731 and 732. The purpose of the questionnaire is to obtain an assessment of a proposed position for which authorization to hold the position is required by 5 CFR Parts 731 and 732. It is the responsibility of the employee/applicant to prepare the 2 Form OPM SF85P Fill Online, Printable 2 Form OPM SF85P Fill Online, Printable 2 Form OPM SF85P Fill Online, Printable Form SF85P: Request for Investigation of Post–Employment Information — Post–Employment Security Investigation (OPM) 2 Form OPM SF85P Fill Online, Printable 2016-02 Questionnaire for Public Trust Positions SF85P. 2 Form OPM SF85P Fill Online, Printable, Fillable Please see your manager to ensure that you provide all required documentation required for approval of your application. If you have any additional questions, contact them, so they can assist you with the Form OPM processing time — SF85P Public Citizen Report — Security Clearance Applications This document documents key elements of the process you take to become a federal security clearance holder. It also documents many of the rules and requirements regarding government employees and the Department of Defense system. This version was created in the early years of the new security clearance system; the information within it reflects current best practices.
online solutions help you to manage your record administration along with raise the efficiency of the workflows. Stick to the fast guide to do OPM Sf 85p, steer clear of blunders along with furnish it in a timely manner:
How to complete any OPM Sf 85p online: - On the site with all the document, click on Begin immediately along with complete for the editor.
- Use your indications to submit established track record areas.
- Add your own info and speak to data.
- Make sure that you enter correct details and numbers throughout suitable areas.
- Very carefully confirm the content of the form as well as grammar along with punctuational.
- Navigate to Support area when you have questions or perhaps handle our assistance team.
- Place an electronic digital unique in your OPM Sf 85p by using Sign Device.
- After the form is fully gone, media Completed.
- Deliver the particular prepared document by way of electronic mail or facsimile, art print it out or perhaps reduce the gadget.
PDF editor permits you to help make changes to your OPM Sf 85p from the internet connected gadget, personalize it based on your requirements, indicator this in electronic format and also disperse differently.
Video instructions and help with filling out and completing Sf 85p processing time 2017-2025